Fast, Scalable, Affordable
Transparent, High Performance Encryption for Kubernetes Environments
Zettaset delivers software-defined encryption for today’s software-defined world. Organizations across all industries choose XCrypt™ encryption solutions because they’re designed to function with near-zero latency to support the most demanding deployment requirements across physical, virtual, and cloud infrastructures.
- Software-based for simple, fast deployment with no proprietary appliances needed
- Works with your existing hardware and requires no specialized encryption expertise
- High-performance, infinitely scalable, low latency, and budget-friendly
XCrypt Kubernetes Encryption is a first-of-its-kind, software-only encryption solution that protects data-at-rest across Kubernetes environments. It provides a transparent, high performance layer of security that will protect your data no matter where it resides, as well as help your organization efficiently transition from DevOps to DevSecOps.
The challenges of data protection in Kubernetes environments
It’s easy to see why Kubernetes is said to be “taking over the world,” especially when a recent CNCF study found that 78% of respondents were using Kubernetes within their enterprise. Although it’s a phenomenal platform for container orchestration and management, Kubernetes does not address one of the most critical components of an overall security strategy – data protection.
Kubernetes Secrets may enable you to securely store and manage things like passwords or tokens, but what about your sensitive data? It’s an important question to ask because Kubernetes environments are like the wild west when it comes to data storage and access. Kubernetes runs your containers where it makes the most sense, so you may not always know where sensitive data is being used or if a given container has access to data that it shouldn’t.
In Kubernetes environments, there’s a lot more possibility for the wrong data to be in the wrong place and that means data protection must be approached differently. As Kubernetes environments are often multi-tenant, granular data at rest protection integrated directly into Kubernetes storage layer is the only way to address security vulnerabilities unique to Kubernetes deployments. It’s for this reason that XCrypt Kubernetes Encryption was developed.
The challenges of transitioning to DevSecOps
IT leaders are finding that integrating security into new technologies being used within DevOps – like container software and Kubernetes – is not keeping pace with continuous software development. Traditional approaches to security and manual controls are often perceived as an impediment to speed, so many organizations push forward without the appropriate levels of security or data protection in place to get to market faster.
However, this is changing as the DevSecOps trend continues to gain momentum. Leaders are looking for ways to embed security throughout their DevOps pipeline to take the ownness of security away from developers. With XCrypt Kubernetes Encryption, developers can focus on building applications and driving innovation without worrying about compromising your organization’s overall security posture.
Kubernetes protects your “secrets.” XCrypt protects your data
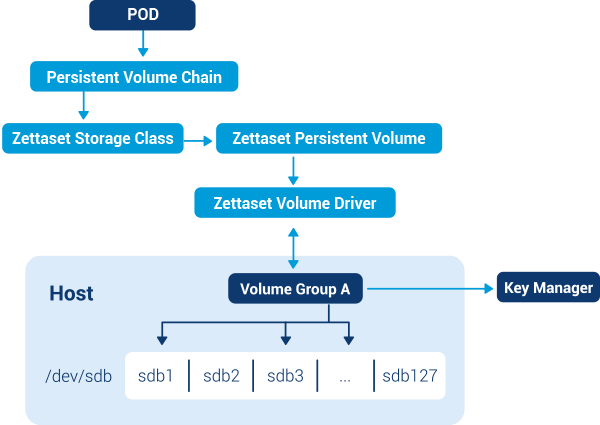
XCrypt Kubernetes Encryption is a software-only solution built specifically to protect data-at-rest in Kubernetes environments. It provides a transparent, high performance layer of security for your entire DevOps pipeline that simplifies data protection while also acting as a ‘last-line-of-defense’ against all the new attack vectors that exist in today’s highly-distributed Kubernetes environments. It integrates directly with Kubernetes’ storage layer and can be deployed without changes to existing processes to enable an efficient, elegant transformation to DevSecOps.
- Direct integration into Kubernetes’ storage layer
- Software-only for simple deployment
- Negligible impact on performance
- Container storage and data separation
- Unique encryption key per each container volume
- Automated encryption policy management
- Secure erase of volumes rather than partitions
Use Cases Include
- Transitioning from DevOps to DevSecOps
- Ensuring data protection in highly-distributed Kubernetes environments
- Achieving compliance in highly regulated industries like healthcare and finance
For more information or to schedule a demo, please email sales@zettaset.com or call 650-314-7920.
Silver member of the